Mayi Nalubega gets arrested for working as a sex webcams model in her own home
The raid was conducted, without any formal process or warrant. Ms. Nalubega was allegedly gang raped while in detention and "bailed out" by her family the next day after they paid millions in Ugandan sheilings to her very rapists to get her out.
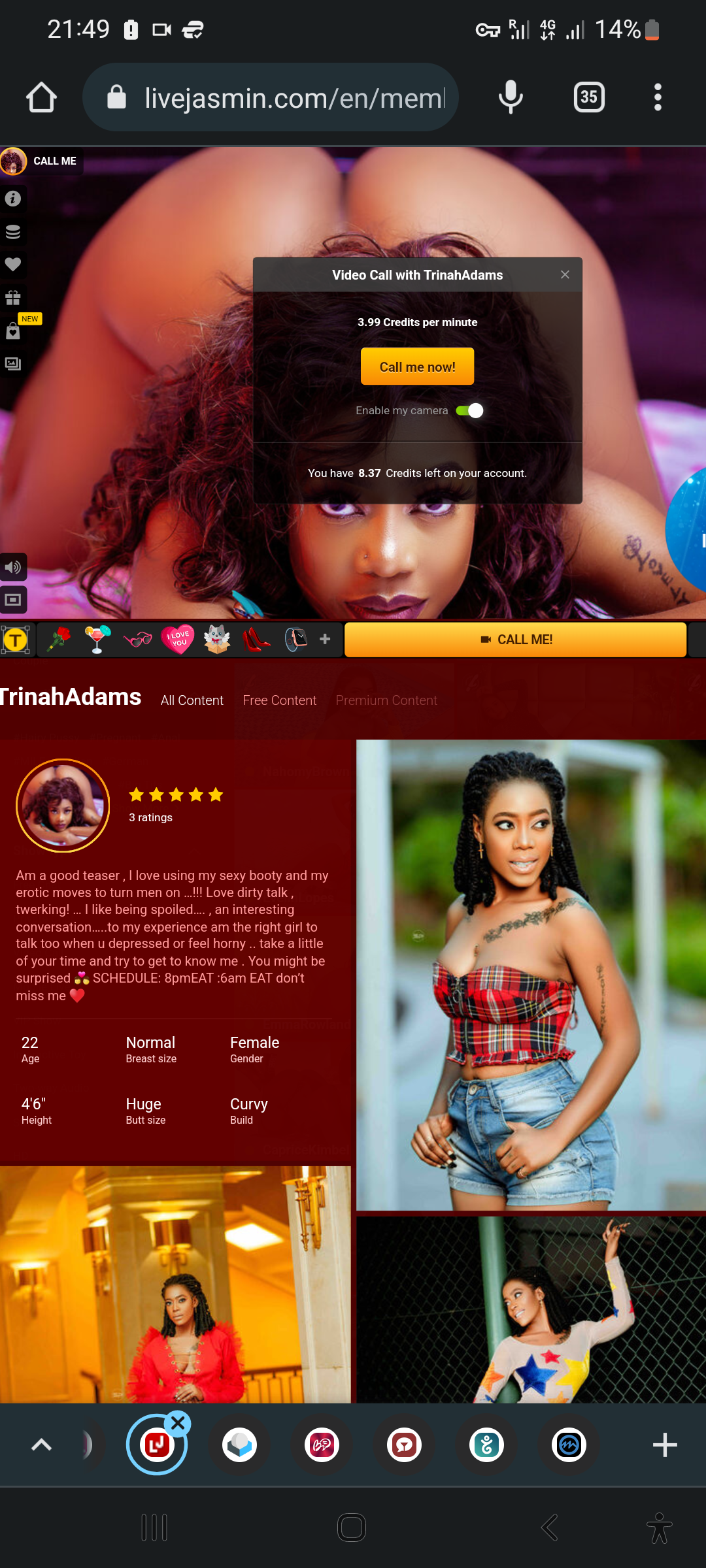
The WhatsApp status Maya posted right after she was released from Police detention, the day after her arrest - No Comment! (BELOW)

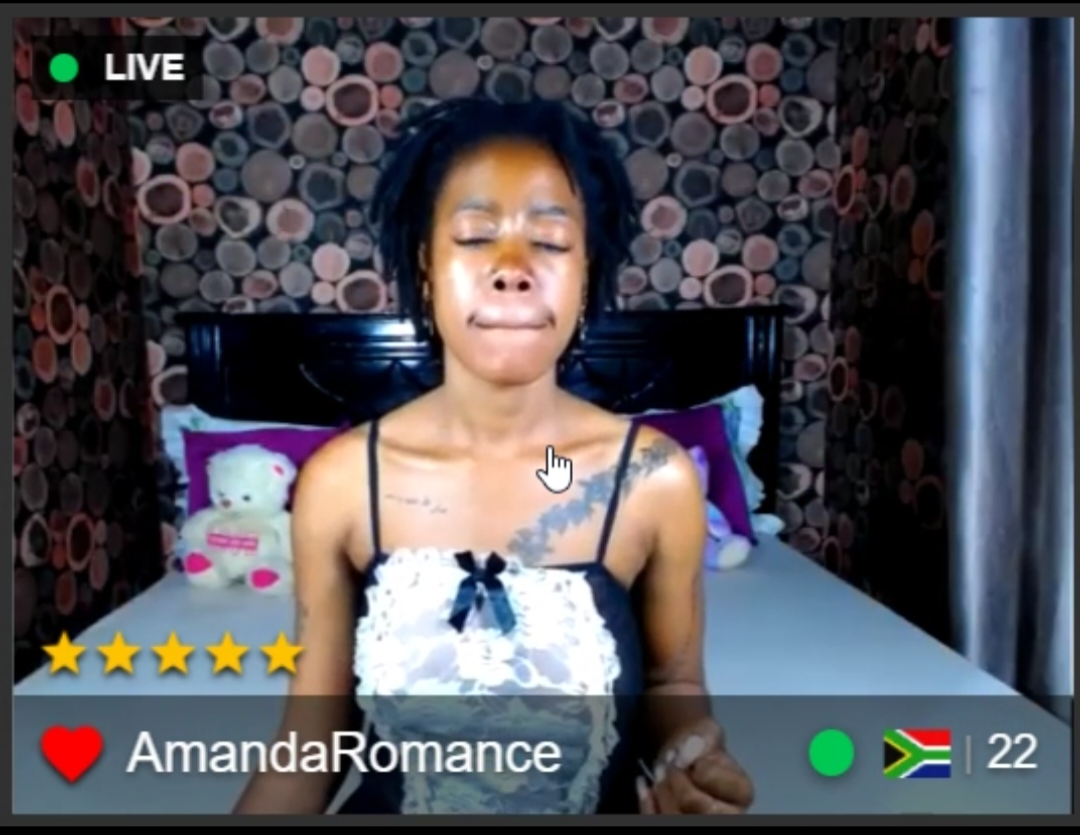
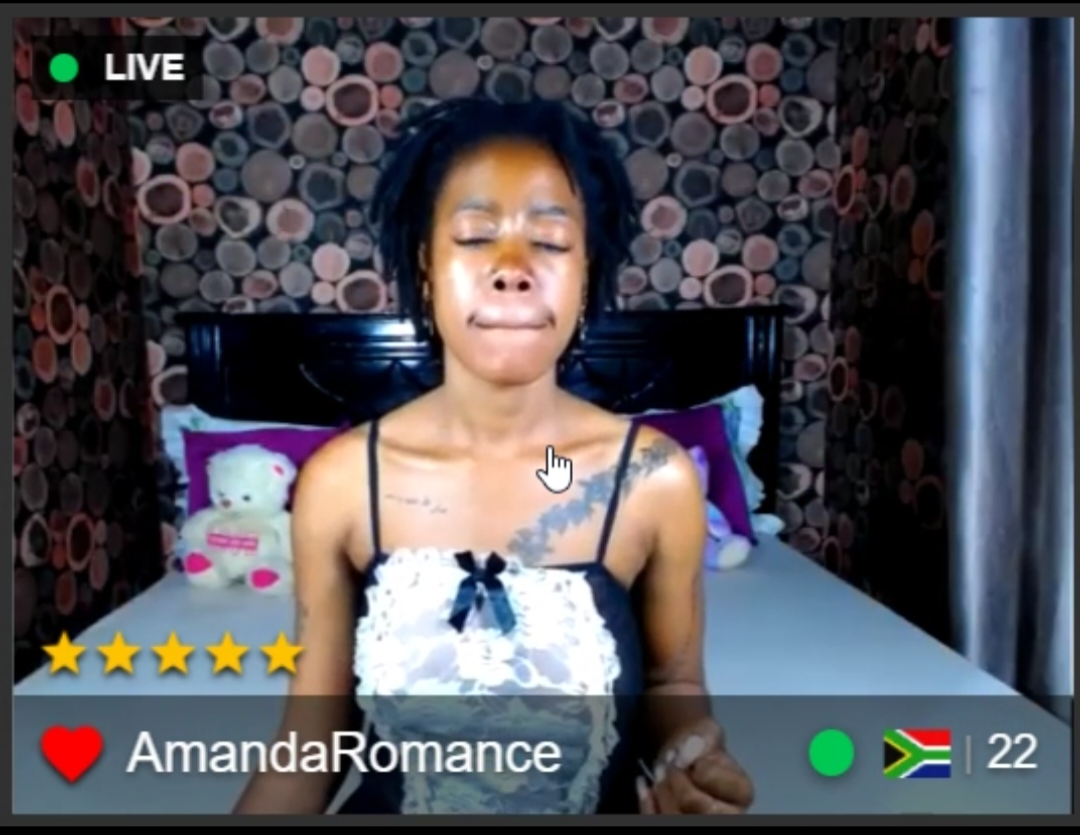
Maya working on streamate.com #1 (BELOW)
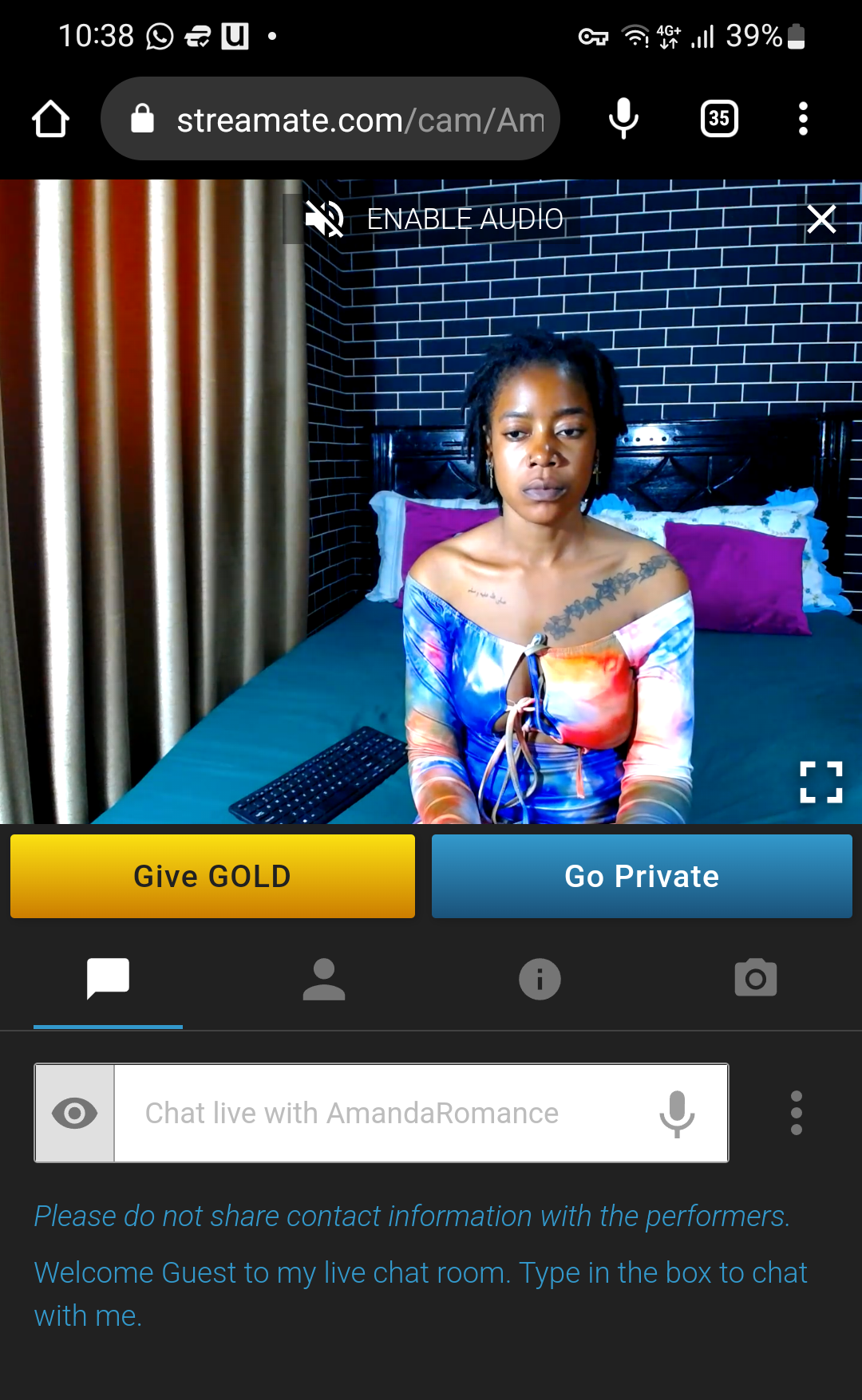
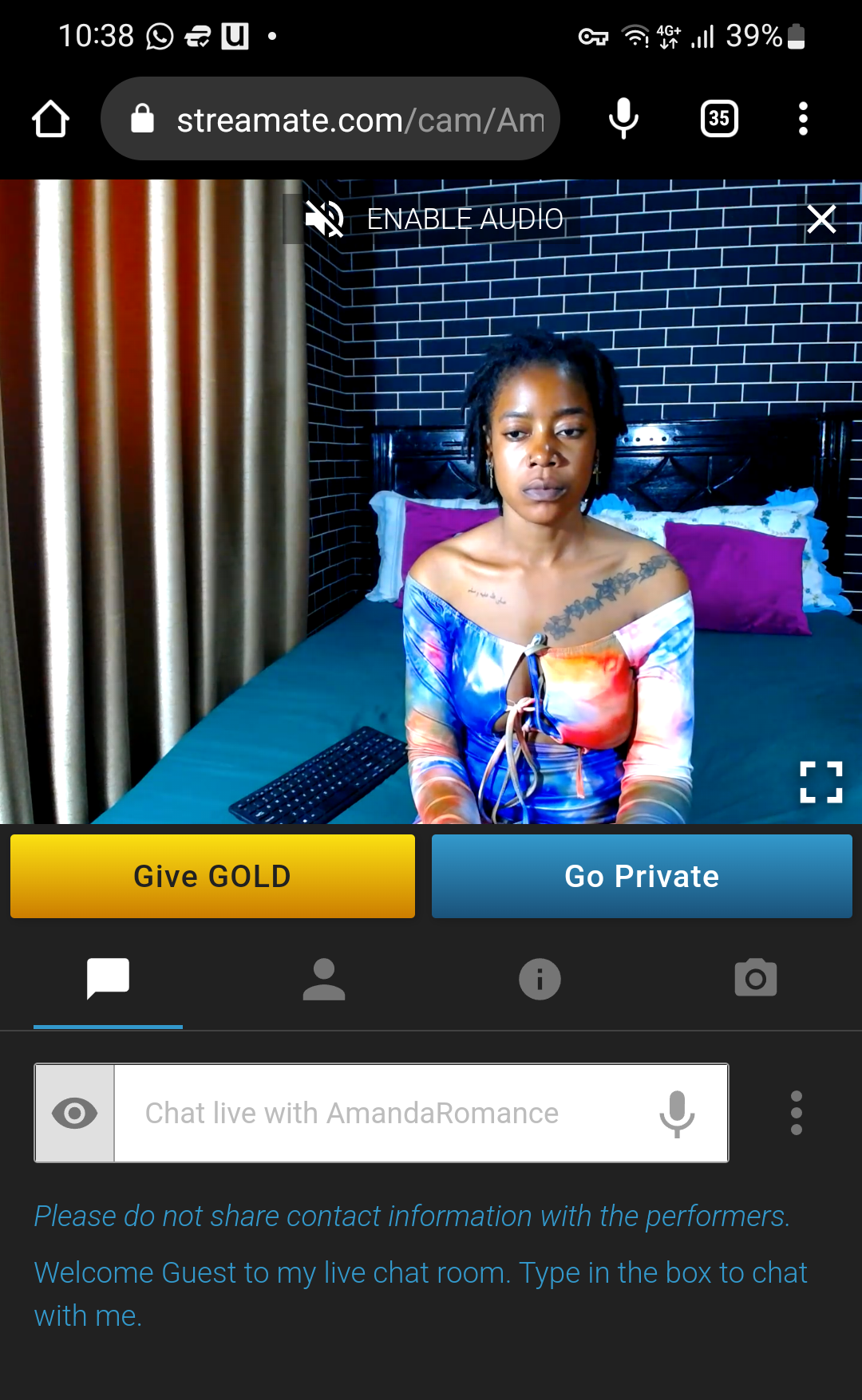
Maya working on streamate.com #2 (BELOW)
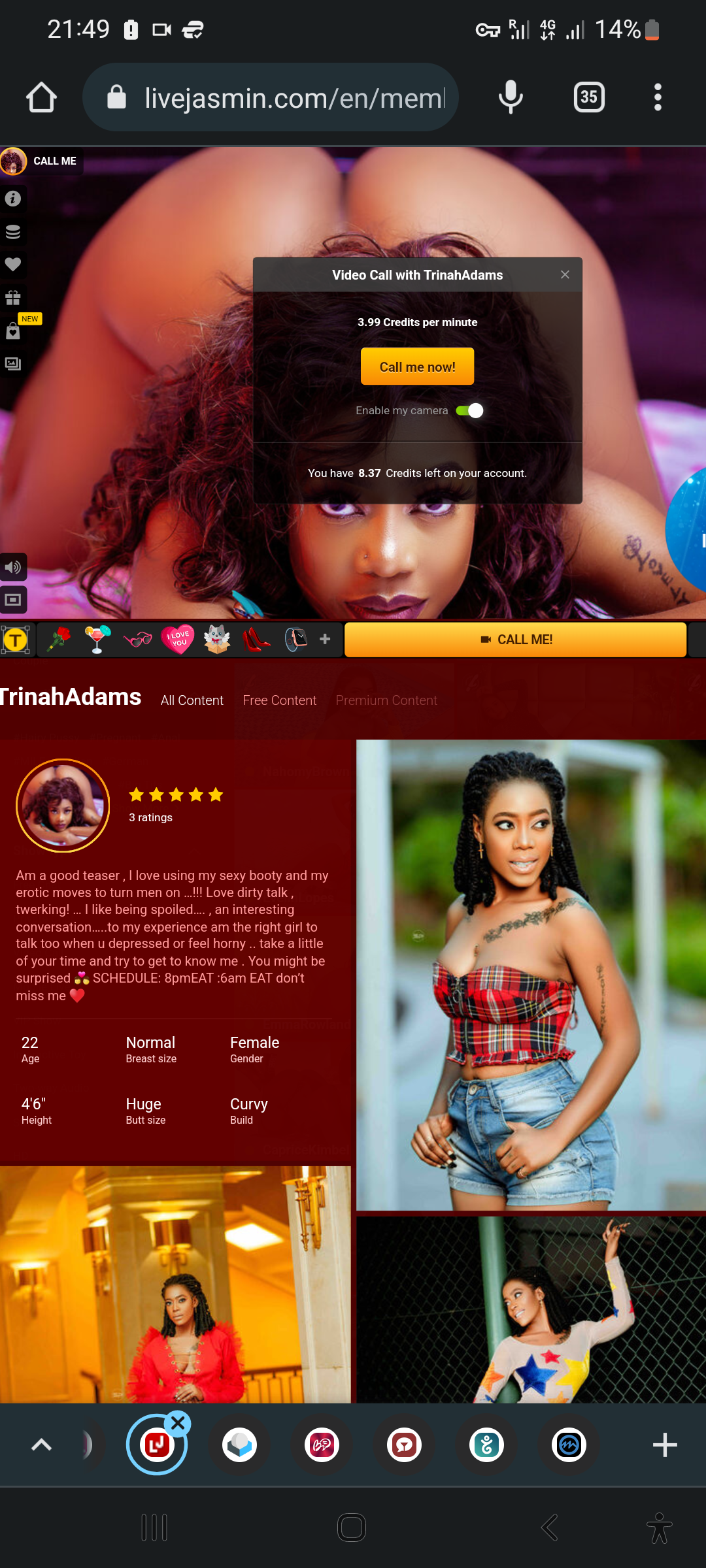
Maya profile on livejasmin.com (BELOW)